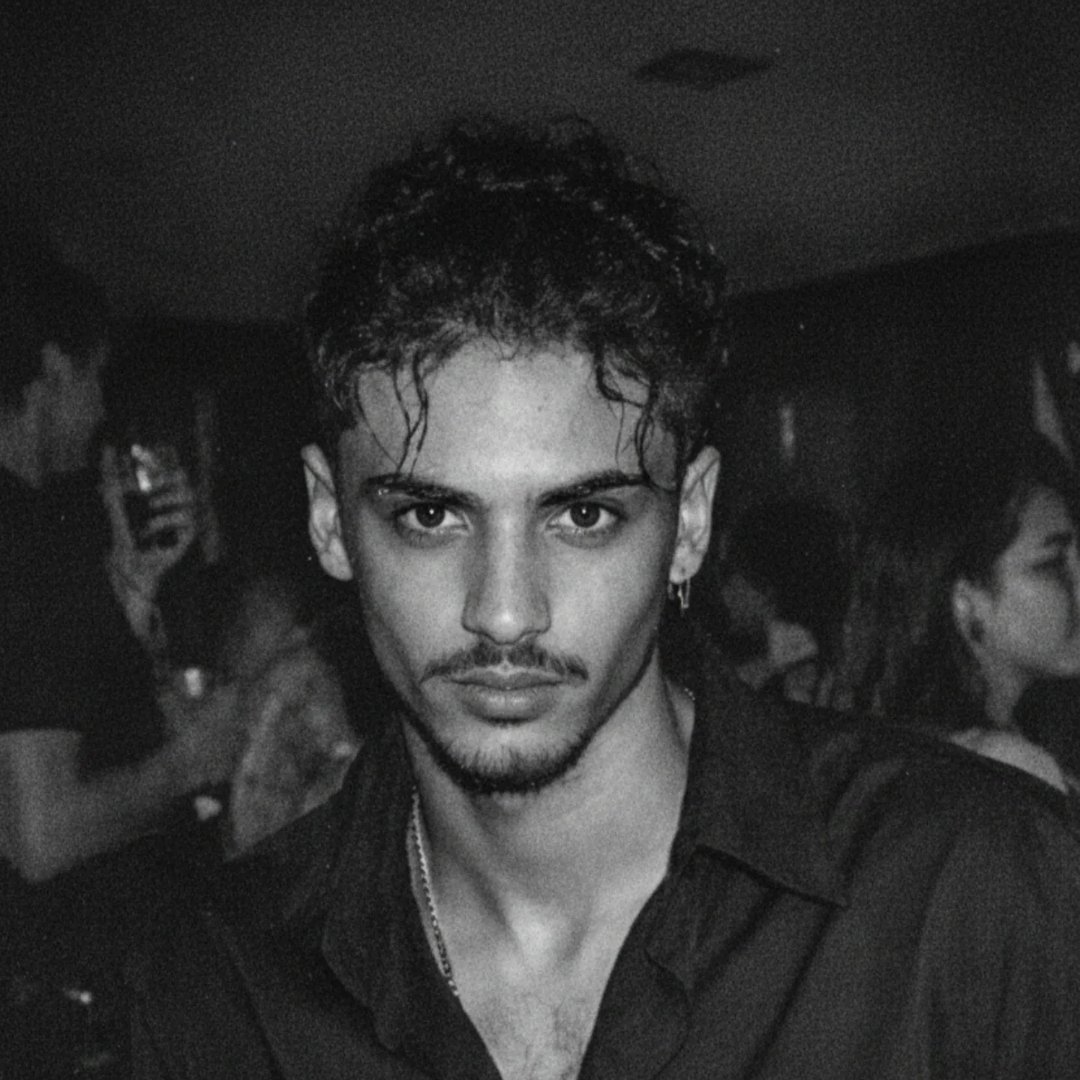
Adam El Adeb
Security researcher with deep focus on AI-assisted vulnerability detection. Engineered custom reverse engineering models to automate defect discovery in compiled binaries.
Work has directly contributed to securing the internet ecosystem, including 4 confirmed vulnerabilities in Google Open Source projects and multiple critical severity CVEs in Industrial Control Systems. Helped more than 400 companies secure their data.